
NetworkManager unfortunately doesn’t have a kill switch in case your VPN connection drops but you can achieve the same effect through firewall rules. I’m using ufw here but you can achieve the same using iptables or firewall-cmd. I haven’t looked into automating this when VPN connects yet but opening Gufw and switching the profile hasn’t become annoying yet either. If I ever get around to that I’ll post an update.
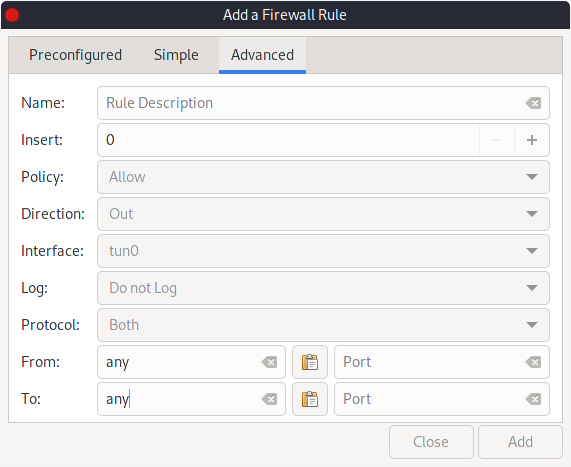
Gufw’s UI is very good and the advanced tab in it’s rules creator has everything I need: interface, direction, to/from IP and port ranges so I use that over setting rules from the command line.
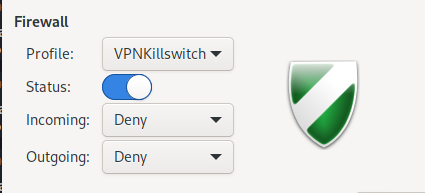
- First, set up the kill switch profile to easily turn rules on and off as needed. You’ll want to set incoming and outgoing to deny:
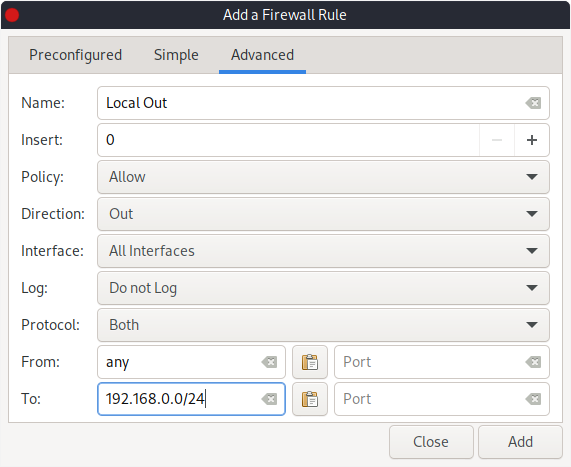
- Optionally, create rules to allow traffic out (and in from if you like) to the local network. You can use CIDR notation here to add your whole subnet:
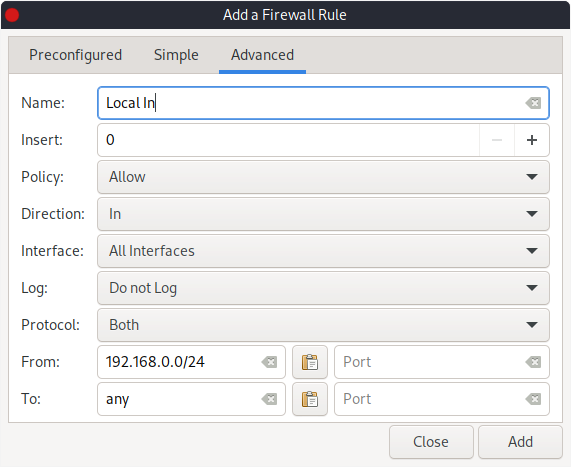
- If you would like to allow local traffic into your machine be sure to switch your from to be your local CIDR and your
toto beany:
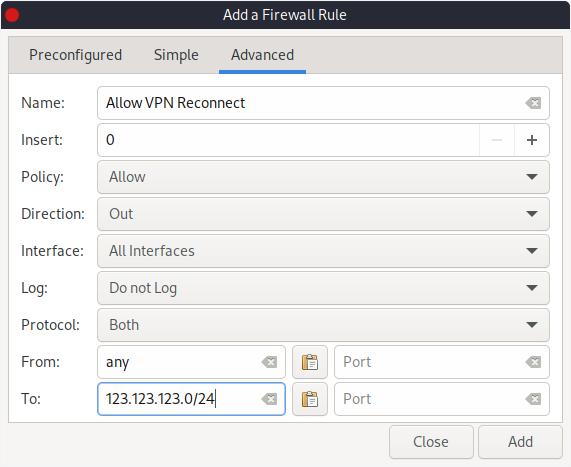
- In order for your VPN to be able to reconnect if the connection drops,
allowany connections out to your VPN servers:
- Finally,
allowany traffic out (and in if you like) on thetun0interface. Since we’re blocking all traffic by default this rule is the magic that makes sure that only VPN traffic makes it out (or in):
That’s it! If you’ve used a VPN client with a kill switch before, ultimately this is how it works under the hood. They’ll have some automation on top to only apply these rules when the VPN is active but the concepts are the same.